Documentation Index
Fetch the complete documentation index at: https://docs.chargeblast.com/llms.txt
Use this file to discover all available pages before exploring further.
Headers
Body
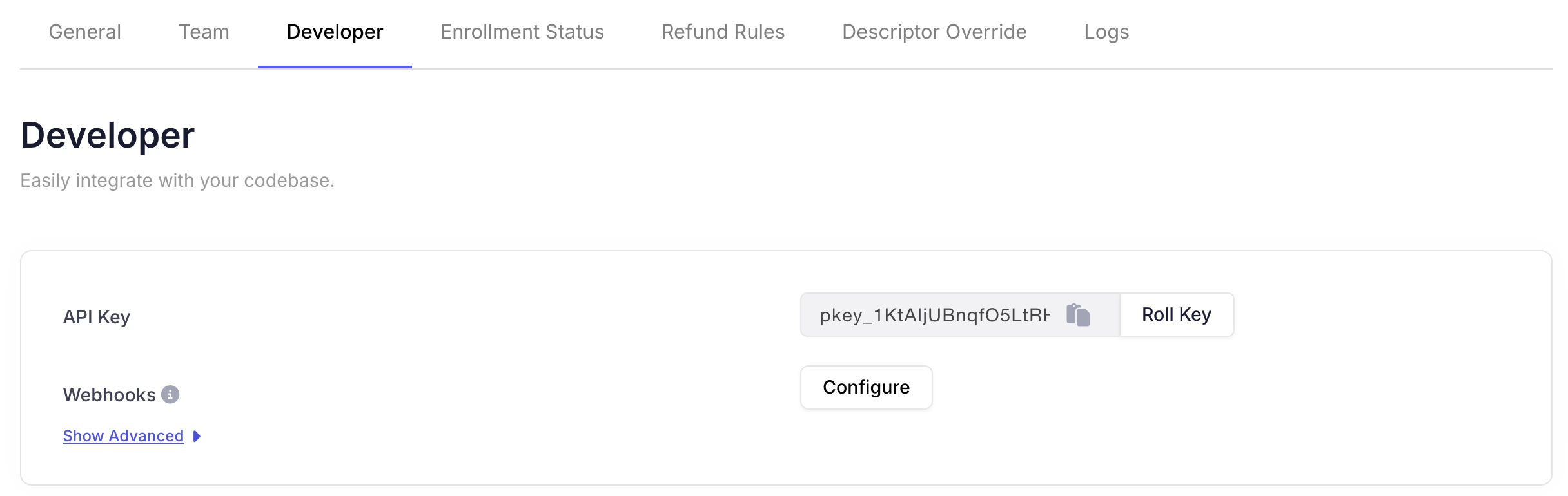
First set up your webhook URL in the Chargeblast dashboard in the settings tab.
The
externalOrder field is not available in the alert.created event.
Please use the alert.updated event if you require this field.Authentication
To authenticate the integrity of incoming webhooks, a header is passed into the post request to your endpoint under the header namesvix-signature. The value in this header is an HMAC-SHA256 encoded string using the payload of the request with the webhook secret as key.
In order to authenticate the request, you perform a HMAC-SHA256 encoding using a concat of webhook request body, svix_timestamp and svix_id and your webhook secret (whsec_xxxxxxxxxxxx) and ensure these strings match. Then input string to SHA256 HMAC will look like:
signedContent = "${svix_id}.${svix_timestamp}.${body}"
This is a common method for ensuring that the webhook messages you receive in your server are from a trusted source and haven’t been tampered with.
bm9ldHUjKzFob2VudXRob2VodWUzMjRvdWVvdW9ldQo=.
Types
Chargeblast emits severalX-Event-Type values (for example alert.created, alert.updated, alert.refunded, alert.matched, alert.will_expire, alert.within_refund_rules). The guide below documents which alert types apply to each webhook event (for example whether Ethoca, CDRN, RDR, or TC40 can trigger that event), when each event fires, and deduping behavior:
Webhook event types
Related
- Webhook event types — Full event-type reference (which of Ethoca, CDRN, RDR, TC40 apply per event)
- Alert Types — Full list of alert networks and subprovider values
- Reason Codes — Codes used when actioning alerts