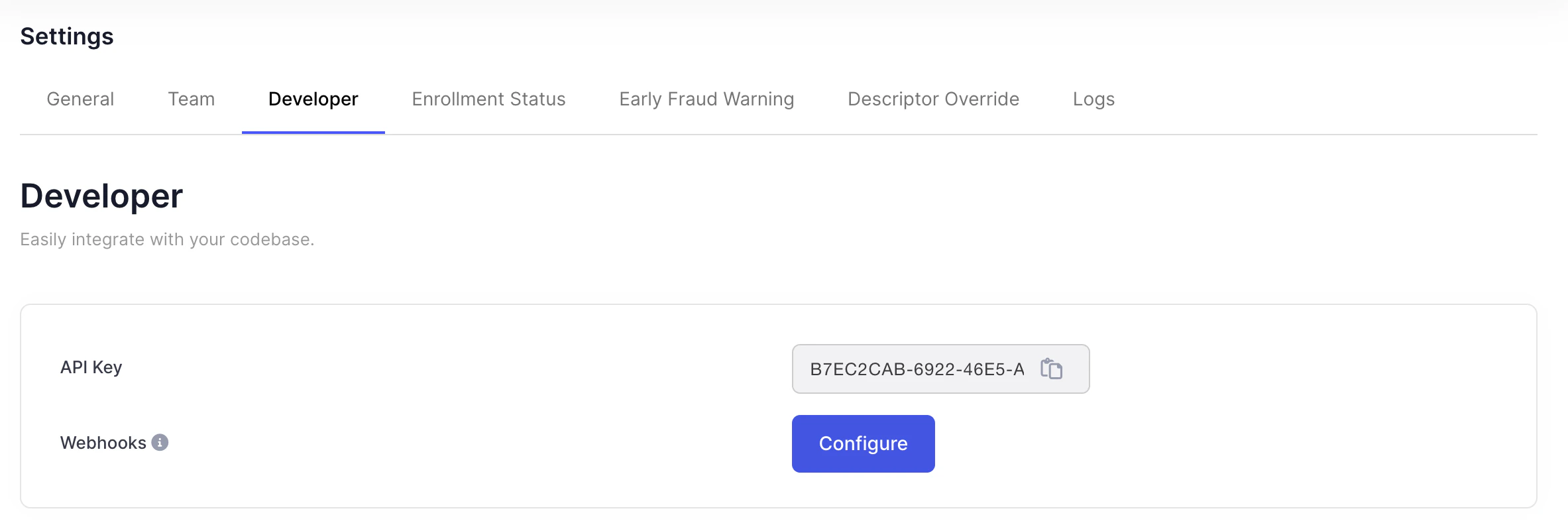
Authentication
To authenticate the integrity of incoming webhooks, a header is passed into the post request to your endpoint under the header namesvix-signature. The value in this header is an HMAC-SHA256 encoded string using the payload of the request with the webhook secret as key.
In order to authenticate the request, you perform a HMAC-SHA256 encoding using a concat of webhook request body, svix_timestamp and svix_id and your webhook secret (whsec_xxxxx) and ensure these strings match. Then input string to SHA256 HMAC will look like:
signedContent = "${svix_id}.${svix_timestamp}.${body}"
This is a common method for ensuring that the webhook messages you receive in your server are from a trusted source and haven’t been tampered with.
PythonJavaScript
`const crypto = require(‘crypto’);
const signedContent = ${svix_id}.${svix_timestamp}.${body};
const secret = “whsec_xxxxxxxx”;
// Need to base64 decode the secret
const secretBytes = Buffer.from(secret.split(’_’)[1], “base64”);
const signature = crypto
.createHmac(‘sha256’, secretBytes)
.update(signedContent)
.digest(‘base64’);
console.log(signature);
`
The svix-signature header is composed of a list of space delimited signatures and their corresponding version identifiers. The signature list is most commonly of length one. Though there could be any number of signatures. For example:
v1,g0hM9SsE+OTPJTGt/tmIKtSyZlE3uFJELVlNIOLJ1OE= v1,bm9ldHUjKzFob2VudXRob2VodWUzMjRvdWVvdW9ldQo= v2,MzJsNDk4MzI0K2VvdSMjMTEjQEBAQDEyMzMzMzEyMwo=
Make sure to remove the version prefix and delimiter (e.g. v1,) before verifying the signature.
Types
For the full list of webhook event types (alert.created, alert.updated, alert.refunded, and others), when they fire, and which alert types apply, see Webhook event types. Prefer the Webhooks guide for the current payload schema and verification steps.